 The hint that spawned an investigation into Italian police officer Dino Maglio, over accusations he had drugged and raped young female travelers, transpired over Italy’s first whistleblowing platform: Irpileaks, based on GlobaLeaks Whistleblowing Software.
The hint that spawned an investigation into Italian police officer Dino Maglio, over accusations he had drugged and raped young female travelers, transpired over Italy’s first whistleblowing platform: Irpileaks, based on GlobaLeaks Whistleblowing Software.
Maglio allegedly lured women to his home by using the popular online hospitality exchange couchsurfing.com.
“An alleged victim came across the platform and sent the leak,” Alessia Cerantola, board member and reporter for the Investigative Reporting Project Italy (IRPI) told a room of two dozen journalists at the 9th Global Investigative Journalism Conference in Lillehammer, Norway.
“This is a good indication that leaks are working,” Cerantola said.
The leak sparked a year-long investigation unveiling at least 14 other young women from around the world who shared similar stories about an Italian police officer who used the website, resulting in a unique transnational collaboration between news publications.
“The challenge now is increasing the culture of whistleblowing in the country,” she said.
Investigative journalism would cease to exist without confidential sources. By building a secure platform for leakers, journalists can create an environment that encourages people to come forward to expose wrongdoing on a multitude of levels while still feeling safe.
A publication that was essentially born out of leaks, The Intercept, founded by Laura Poitras, Glenn Greenwald, and Jeremy Scahill, has been dedicated to source protection since it launched in 2014. Initially, it focused on reporting out the documents leaked by NSA whistleblower Edward Snowden; it has since expanded its coverage but maintained its core mission: to hold governments and corporations accountable through fearless and adversarial journalism, a task which would be virtually impossible without a safe, user friendly platform for sources to leak information.
“SecureDrop is a piece of software that lets sources anonymously and hopefully securely send us messages and documents,” explained Micah Lee, technologist and SecureDrop developer for The Intercept.
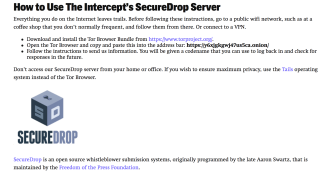
In order to build a SecureDrop platform in your newsroom, he said, there are several requirements. First, the client needs two servers: one server for SecureDrop and another server used to monitor SecureDrop for suspicious activity. Hosting the server in house is crucial. The first step in the event of a leak investigation will be for the authorities to identify how the source contacted the journalist, and if they can identify where the SecureDrop is hosted, they’ll be able to send data requests to the service provider which could lead to clues that could compromise the safety of the source.
Beyond the servers, the journalists will need two computers: one computer that can connect to the internet and one “air-gapped” (physically isolated) computer that stays completely apart from all networks. When a source submits a document or message via SecureDrop, the journalist will use a USB stick with the privacy-enhancing Tails operating system to download the encrypted message from the first computer (the one with internet). In order to safely de-crypt the message, the journalist will need to plug the USB stick into the air-gapped computer (the one without internet).
While SecureDrop is a useful tool for the source, juggling multiple computers, USB sticks and memorizing various pass phrases can make it a headache for the journalist. But in order to simplify the workflow it would require usability and security tradeoffs, and security tradeoffs aren’t really an option if you’re dedicated to protecting your source. So to make things easier at The Intercept, Lee explained, there is a small group of people solely dedicated to checking SecureDrop day-to-day and analyzing submissions. Those people then assign each submission to the appropriate journalist.
“If source is taking big risk and isn’t very tech savvy, these platforms help a lot,” Lee said.
But even with a platform like SecureDrop, if there is a risk that you could become a suspect after a story is published, there is more you need to do in order to make sure the trail does not lead back to you.
For operational security advice, Lee wrote an article, “How to Leak to the Intercept,” in which he provides information for sources about how they can maintain anonymity beyond SecureDrop. Lee outlines what not to do, what to worry about, and details how to actually leak.
“It sounds complicated, and it is.” Lee writes. “But if you’re risking a lot, it’s probably worth the effort.”
Abby Ellis reports on this event as part of the IACC Young Journalists Initiative, a network reporting on corruption around the globe.
